- Using mobile banking?
- Having already a lot of apps and worried about installing another one?
- Do you want to be sure that your data on your phone is protected?
Raw Control has been designed for you
Incorporating the advanced telemetry data analysis, without compromising your privacy, we detect the threats and notify you immediately after they are detected. You are provided suggestions what to do to stay safe online when using your smartphone. The app has no access to your private data in any situation.
How it works?
Main functionalities
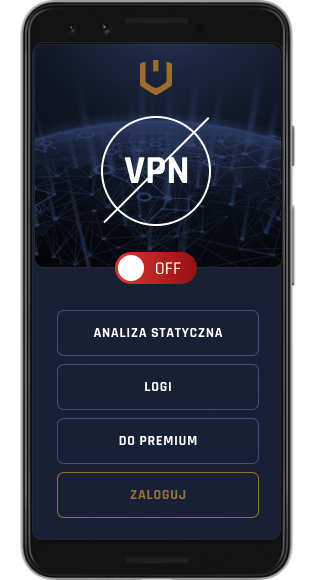
RAW Control provides the following safety functions to the device on which it is installed:
Automatic VPN configuration and the outbound traffic inspection. The URL screening and endpoint classification.
The traffic is redirected to the RAW infrastructure – a detailed outbound traffic inspection is conducted by automated mechanisms and SOC analysts in RAW. The anomalies and suspicious connections are identified – in case of detecting malware the user is notified immediately to undertake countermeasures.
Controlling passcode protection of the lock screen.
A home screen protection is the fundamental mechanism protecting the smartphone user from the unauthorized access if the device is lost or stolen. No screen lock is a serious mistake which, if corrected, significantly increases the user security.
Checking the device attestation including:
- Jailbreak detection
- Debugger mode detection
- Reverse engineering framework detection
Device integrity is one of the key components proving that the device has not been hacked - RAW Control monitors multiple elements related to the permission system and attestation profile to verify the operating system consistency and that no suspicious tools indicating hacking activity is present.
Dashboard with alerts and reports:
- Automatically generated
- Monthly created by our analyst after examining the traffic on the device
- Occasionally prepared by our analyst about the current threats and attacks
The user is sent the information about the threats along with the guidelines what to do. On a monthly basis the SOC RAW analyst will review the logs and the issues reported and will prepare a dedicated threat analysis for the user. In case of detecting serious risks the user will be contacted by phone to discuss the situation. The user will be kept informed by the SOC RAW in the event of emerging information about the hacking campaigns or attacks.